Website running slow? How to get it running quickly
If your WordPress website is feeling sluggish, don’t worry—there are a few simple steps you can take to improve performance without diving into technical settings. Is caching enabled on your website? If you are a Globe2 customer – the answer is yes. During your onboarding, we would have provided you with our free optimisation service during your […]
Why Keeping Your Router Updated Is Essential for Business Cybersecurity

Security as Standard When it comes to securing your business network, routers are often overlooked — quietly sitting in the corner, doing their job. But if that router is running out-of-date firmware, it could become the weakest link in your cyber defence. That’s why our Business Broadband package includes a license to the DrayTek ACS3 […]
Cyber Essentials Update: What Home Routers in Scope Could Mean for Businesses

Cyber Essentials is evolving once again, with a new set of certification questions set to take effect on April 28, 2025. These updates reflect ongoing efforts to keep businesses secure amid changing technology and working practices. While we’re still awaiting full details, one update stands out: home routers will now fall within the scope of […]
The Overlooked Importance of Domain Registration: What Every Business Owner Should Know

When was the last time you thought about your domain registration? If your answer is “not recently” or “never,” you’re not alone. Many business owners assume that once a domain is registered, it takes care of itself. However, neglecting your domain registration can lead to serious disruptions for your business, including website downtime, lost emails, […]
Are you still avoiding Windows 11?
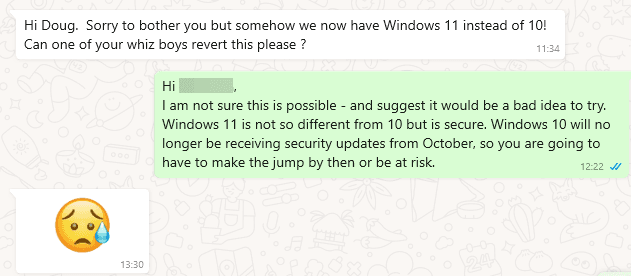
I recently got a message from my mother-in-law saying, “We now have Windows 11 instead of 10! Can you revert this please?” It made me think about those who are avoiding upgrading, and why. With Windows 10 reaching its end-of-life in October 2025, it’s important to consider the benefits of upgrading to Windows 11 and […]
Security Hints & Tips: Email Safety for Small Businesses

Beware of Unexpected Emails In today’s fast-paced business world, we all receive a constant flow of emails—bank statements, order confirmations, sales promotions, and more. It’s easy to quickly skim through your inbox to keep up, but it’s crucial to remain vigilant. Cybercriminals know how to exploit full inboxes and send dangerous, unexpected emails. Unusual Scam […]
Physical 2FA Keys vs. Authenticator Apps: Which Should You Choose?

In an age where cybersecurity threats are becoming increasingly sophisticated, two-factor authentication (2FA) has become a cornerstone of online security. By requiring a second form of verification in addition to a password, 2FA adds an extra layer of protection that can thwart many common attack vectors. Among the most popular methods of 2FA are physical […]
Crowdstrike – lessons to be learned

The Worst Cyber Event In History This July 8.5 million Microsoft devices were hit with a faulty software update – the scale of effects of the disruption caused make this event, which began on 19 July, makes it the worst cyber event in history, beating the WannaCry cyber-attack in 2017 where 300,000 computers in 150 […]
Unlocking Insights: The Benefits of Microsoft Clarity for Your Website

See exactly what your visitors are doing In today’s digital landscape, understanding user behavior on your website is crucial for driving engagement, improving user experience, and ultimately achieving your business goals. One tool that has been gaining significant traction for its powerful yet user-friendly analytics capabilities is Microsoft Clarity. Google Analytics can offer a lot […]
How to Use DMARC and DKIM to Stop Email Spoofing
Email spoofing is a deceptive practice where cybercriminals forge email headers to make messages appear as though they are coming from a trusted source. This tactic is commonly used in phishing attacks to trick recipients into revealing sensitive information or clicking on malicious links. However, with the right email authentication protocols, such as DMARC and […]